Portal26 Offers A Modern Data Security Alternative for Key Products Facing Imminent Retirement
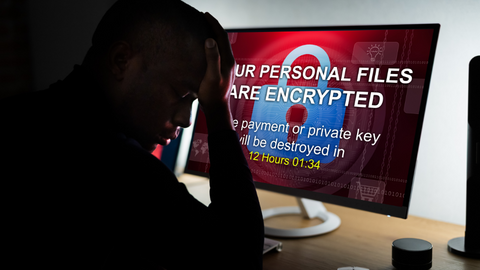
Portal26 Offers A Modern Data Security Alternative for Key Products Facing Imminent Retirement Portal26, the industry’s most sophisticated data security and anti-ransomware platform, rises to the rescue as industry changes force customers to abandon critical pieces of their data security strategy As breaches increase in complexity, there is a significant need among organizations for security […]