Best Practices in Data Tokenization
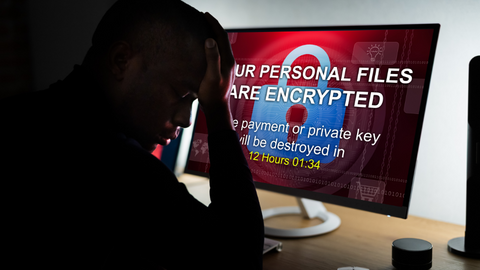
Essential Data Tokenization Best Practices: A Complete Guide Tokenization is the process of replacing sensitive data with unique identifiers (tokens) that do not inherently have any meaning. Doing this helps secure the original underlying data against unauthorized access or usage. Tokenization was invented in 2001 to secure payment card data and quickly became the dominant […]
Best Practices in Data Tokenization Read More »